Looking for a Hnry alternative?
Get better bang for your buck with Reckon accounting software
Reckon One pricing starts from only $12/month, with Hnry you expect to pay up to $125/month!

Get more features for less
Hnry plan vs Reckon One ‘Accounting Plus + Payroll Essentials’ plan.

Unlimited users
Track GST & BAS
Payroll
Pay up to 4 employees
Free onboarding session
STP reporting
Reconcile bank transactions
Budgeting
Unlimited free phone support
Monthly price
1% of your income + GST
$32.00
Reckon One’s unlimited free phone support is available during business hours.
This table is in comparison to Hnry’s standard features. Data correct as of July 2024.
Better value as your business grows
Unlimited invoices
Invoice away, there’s no more to pay! Reckon includes unlimited invoices so you can get paid faster.
Easy payroll software for your employees
Manage payroll starting for just $12/month for up to 4 employees including Single Touch Payroll.
Unlimited admin users
With Reckon, you can give as many people access you like including your accountant, admin staff or family members.
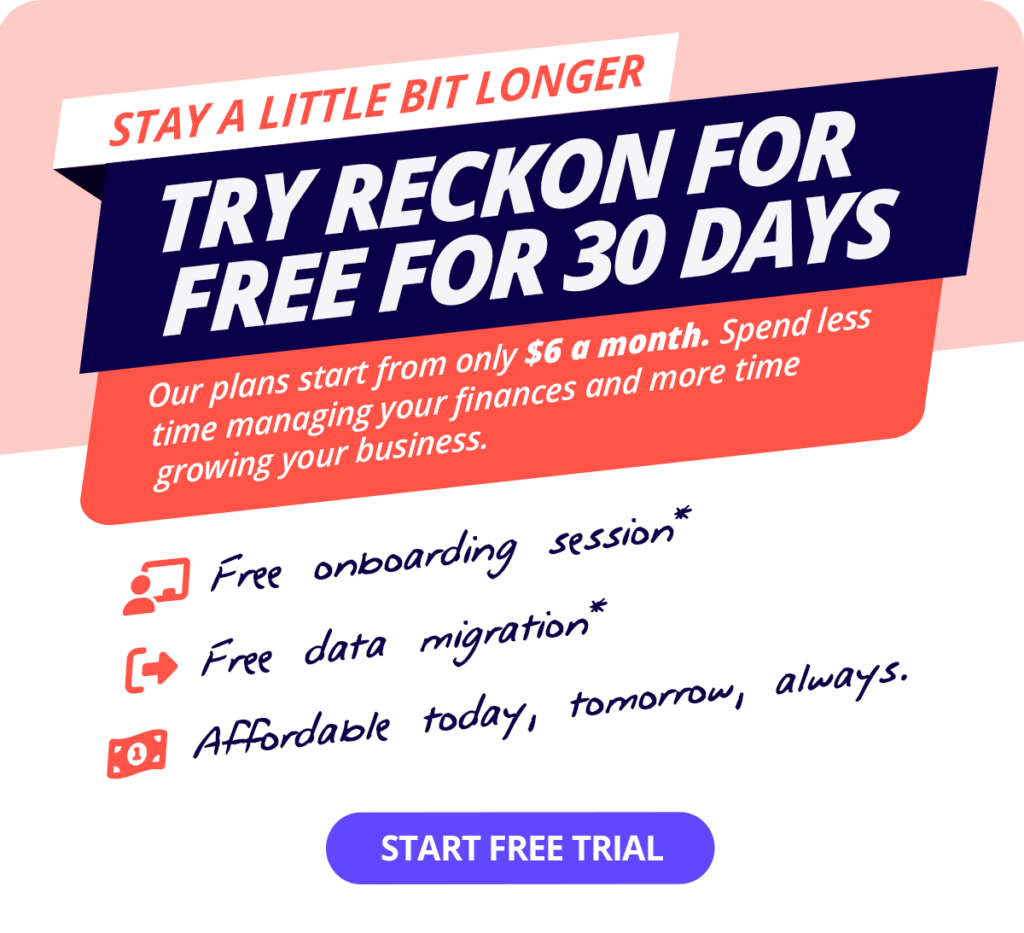
Migrate from Hnry to Reckon for free
Moving your data from Hnry to Reckon is quick and easy with our migration service. It’s free when you sign up for our Reckon Plus or Premium plans.
Affordable accounting for all business sizes
Hnry takes 1% + GST* of your income
And if your business makes more than $150,000 per annum, expect to pay $1500. This does not include payroll functionality or super, meaning you are limited to the services Hnry provides despite your business needs.
Hnry does not allow you to use their service independently, limiting control of your finances!

…While Reckon One starts from just $12 per month
You’ll only pay $12 a month to manage GST, BAS and you income. That’s much cheaper than 1% of your income!
Plus, you can manage all aspects including Payroll with Reckon saving you time and streamlining the technology you use to manage your business.
*Monthly cost of Hnry’s standard accounting plan at the standard price, correct as of July 2024.
There are a million reasons to love Reckon
Convinced Reckon One is the perfect Hnry alternative for small businesses?
Try Reckon One for free, cancel anytime.